About 1-855-260-3658 popup
1-855-260-3658 popup is made to direct tricks on PCs. In spite of the fact that users know that there exists such sort of technical support tricks, they are still swindled to pay it money since it is savvy to exploit users’ worry to their PC and the Internet. When it turns up on the PC, some users should know its genuine nature and they need to pay more attentions on their PCs at this time.
About the principle path for 1-855-260-3658 popup profiting
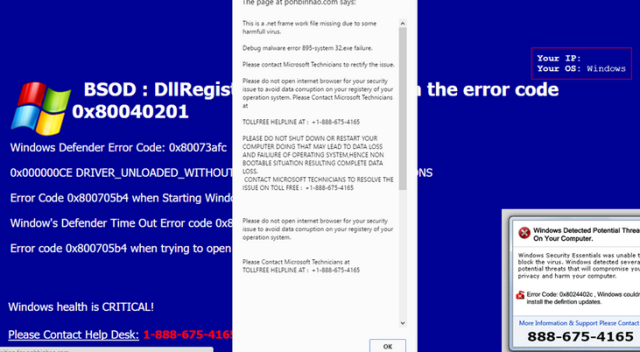
1-855-260-3658 popup is intended to cheat users’ money as you most likely are aware. What’s more, it begins this trick with a PC condition report. It will express the issues that your PC right now endures, for example, virus intrusion, malware infection, browser hijacker tricks, or error mistake. With these things, users will stress over their PC and their data. And after that, they will require helps from it and it profits.
Why should not users require assistance from 1-855-260-3658 popup
Other than the huge measure of money you ought to pay for 1-855-260-3658 popup, you likewise need to give it consent to grasp a hand in your PC. In this way, more harms will be brought on by it but you will need to thank for its assistance. Besides, it can likewise duplicate your information along these lines.
So it is dangerous to seek assistance from 1-855-260-3658 popup. The time has come to uproot it. Here we furnish you with removal guides. Please check them.
1-855-260-3658 popup Briefing |
|
| Type of the Threat | Redirect Virus |
| Simlar Virus or Malware | AUTO-LOADING TRJN, 1800 875 374 pop-up, 1-855-628-1810 |
| Spreading Channels |
|
| Reported As | 1-855-260-3658 scam, 1-855-260-3658 fake microsoft support, 1-855-260-3658 malware, 1-855-260-3658 virus, 1-855-260-3658 popup. 1-855-260-3658 fake alert |
| Troubles Made by 1-855-260-3658 popup |
|
Our experts have worked out the solutions on removing 1-855-260-3658 popup from Windows PC and Mac OS below: Section 1 is for Windows PC Users; Section 2 is for Mac OS Users. Please follow the corresponding solution for your computer OS.
Section 1 – Effective Steps to Get Rid of 1-855-260-3658 popup from Windows PC
Step 1. Uninstall 1-855-260-3658 popup related programs and other unwanted software you installed recently.
1. Press “Windows” key and “R” key at the same time to open “Run” window.
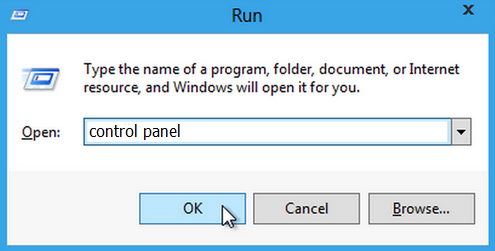
2. As the above image shows, now input “control panel” in the Run window and click OK, then you will see the Control Panel window.
Now select category view, and click on Uninstall a program under the Programs.

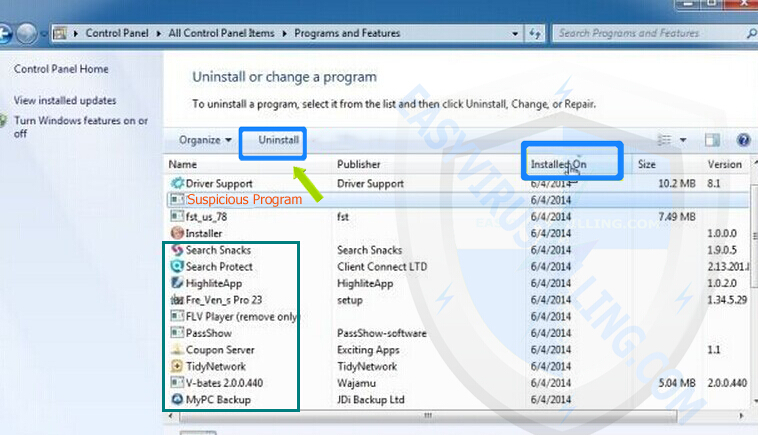
3. Now the Programs and Features window is opened as below.
Please click Installed On to display the latest programs, scroll through the list to find and uninstall 1-855-260-3658 popup and other unwanted programs installed recently.
——————————————————————————————————————————-
If you are a Windows 10 user and cannot execute the steps above, please try this method:
1. Click Start Menu on Win 10 screen, and click All apps.

2. Now you can see all apps of your Win 10, find out the unwanted or suspicious program, then right-click it and select Uninstall.
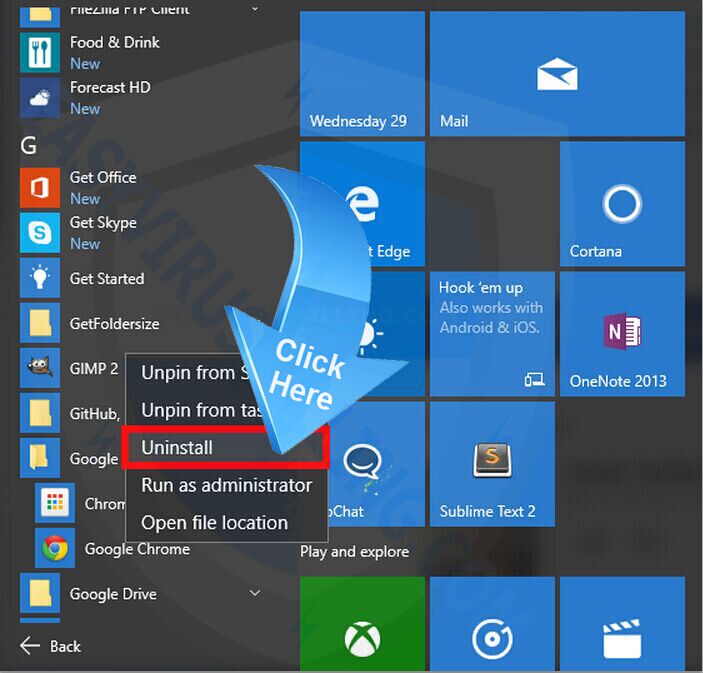
(Note: Please go to next step if you do not find any suspicious program in the list)
Step 2. Remove Microsoft Edge/ Internet Explorer add-on, Chrome extension and Firefox add-on related with 1-855-260-3658 popup.
Microsoft Edge User
(Since Edge browser does not have extensions function now, what you need is just to reset homepage and search engine.)
1. Set your homepage page on Microsoft Edge to remove hijacker virus.
- Select More (…) on the address bar, then Settings
- Under Open with, select A specific page or pages
- select Custom to enter the URL of page you want to set as homepage
———————————————————————————————————————————————-
2 . Set your default search engine to remove search redirect virus.
- Select More (…) on the address bar, then Settings
- Click View advanced settings
- Click <Add new> under “Search in the address bar with”, then input the search engine you like
- Now select the search engine you like and click Add as default
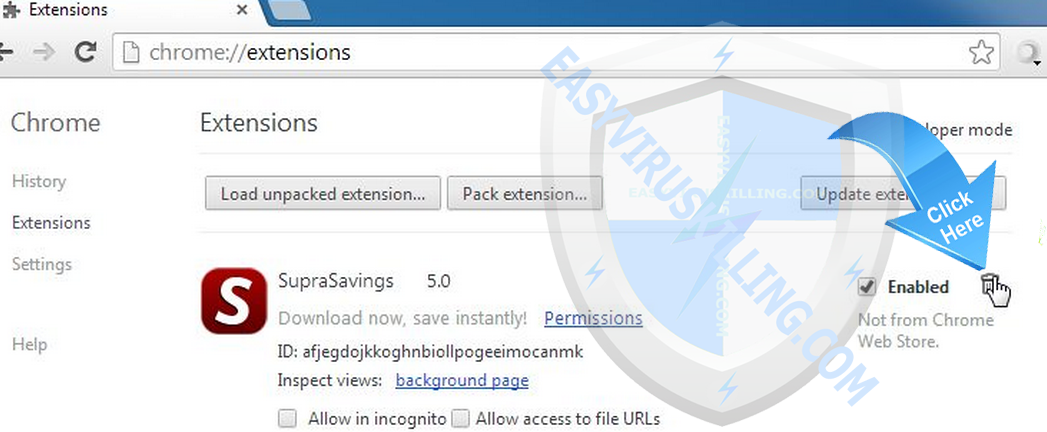
Google Chrome User
- Click the Chrome menu
 on the browser toolbar.
on the browser toolbar. - Click Tools.
- Select Extensions.
- Click the trash can icon
 to delete 1-855-260-3658 popup extension.
to delete 1-855-260-3658 popup extension. - Make sure to remove all extensions you do not know or need.
- A confirmation dialog appears, click Remove.
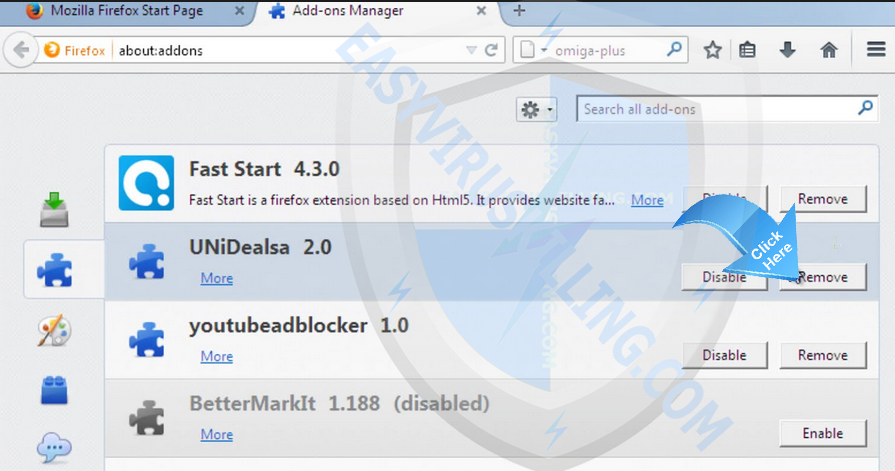
Firefox User
- Click the menu button

 and choose Add-ons. The Add-ons Manager tab will open.
and choose Add-ons. The Add-ons Manager tab will open. - In the Add-ons Manager tab, select the Extensions panel.
- Make sure to remove all extensions you do not know or need.
- Click Disable or Remove button of 1-855-260-3658 popup.
- Click Restart now if it pops up.
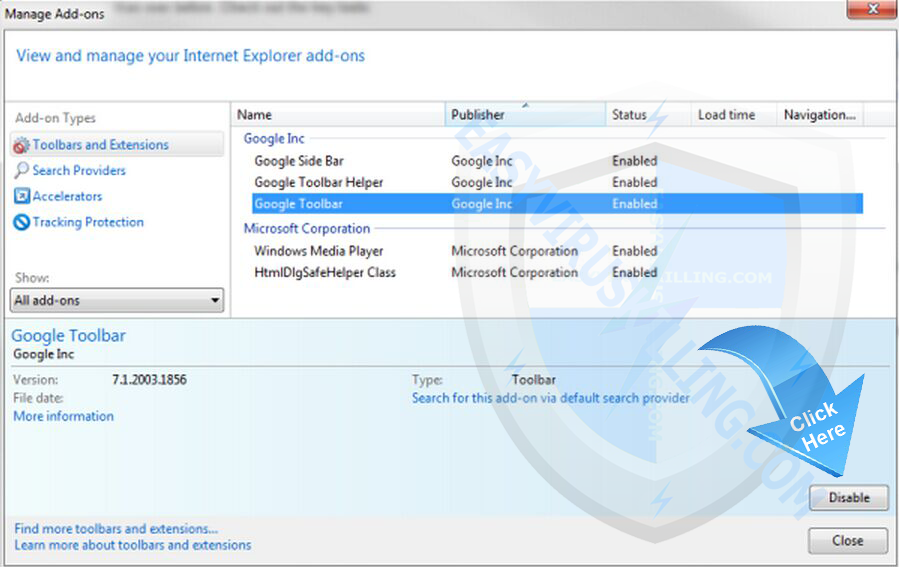
Internet Explorer User
- Open the IE, click the Tools button

, and then click Manage add-ons.
- Click Toolbars and Extensions on left side of the window., and then select 1-855-260-3658 popup
- Make sure to remove all BHO’s you do not know or need.
- If the add-on can be deleted, you’ll see the Remove option. Click Remove and then click Close. Otherwise click Disable button.
Step 3. Diagnose your computer with SpyHunter and remove 1-855-260-3658 popup and other viruses (Important Step)
SpyHunter is best of the best AntiSpyware/ AntiMalware tool capable of detecting and removing all the Adware, Spyware, Malware, PUP, and Trojan Horse hiding in Windows computer. Start a free scan with SpyHunter now and find out all malicious files related with 1-855-260-3658 popup virus.
1. Click this link: “Download SpyHunter” or the blue button below to download SpyHunter safety:
Tips: After SpyHunter is downloaded, your Chrome /Firefox /IE may display such fake security warning ” This type of file can harm your computer. Do you want to keep Download_Spyhunter-Installer.exe anyway?”, which is generated by virus to cheat you, please just ignore the fake warning and click “Keep” button.
(Notes – If you do not need it any more, please follow instructions on SpyHunter uninstall. SpyHunter`s free version provides unlimited free scans and detection. After it detects malicious files, processes and registry entries, you can follow the scan results to manually locate and remove them on your own; or to purchase its full version to automatically remove the virus with ease. Meanwhile, the full version of SpyHunter will offers you unlimited one-on-one professional help for any malware related issue by its official PC expert.)
2. Once downloaded, please double-click SpyHunter-Installer.exe to start the installation of SpyHunter.
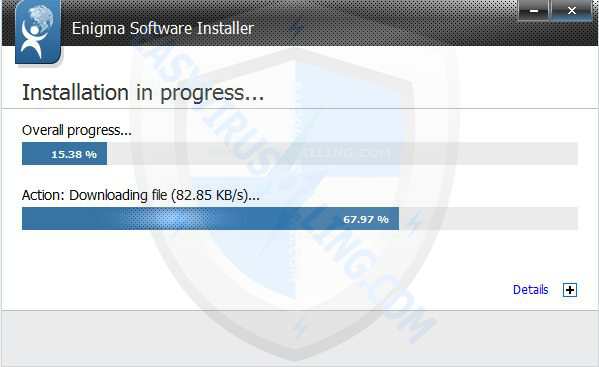
3. When SpyHunter is installed, it will be run automatically, then click Scan Computer Now to detect 1-855-260-3658 popup related threats:
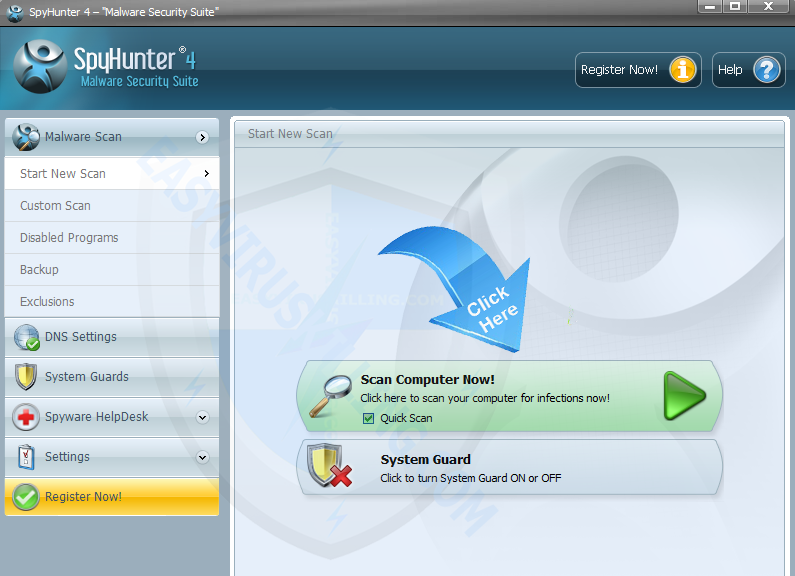
4. Once SpyHunter completes the scan, please click Fix Threats to get rid of 1-855-260-3658 popup.

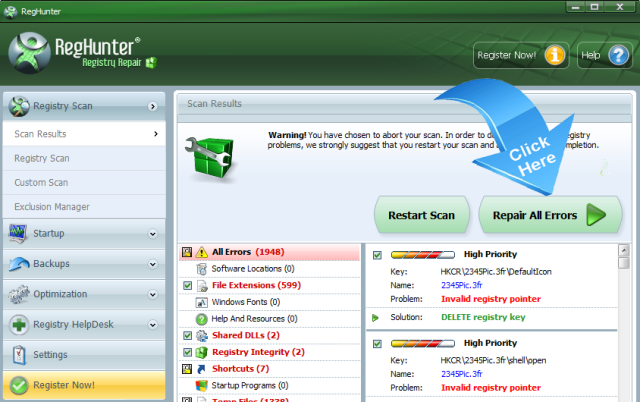
Step 4. Use RegHunter to fix all damaged registry errors and security bugs caused by 1-855-260-3658 popup.
Notes: If 1-855-260-3658 popup virus still appear after you removed it with SpyHunter, it is clear that there are some registry errors and security bugs needed to be fixed. 1-855-260-3658 popup virus can be re-activated by malicious codes it injected into your Registry, therefore we need to fix those registry errors and security codes and recover the healthy system files. After we fix the Registry, 1-855-260-3658 popup will not have any chance to re-activate itself again. When we do any operation related with Registry, we need to be 100% careful, because any small mistake we make in the Registry can lead to severe problems, therefore, we recommend every user to let RegHunter help you complete the complicated operations in Registry automatically. It is one of the best tool which can maximize system performance and fix registry and system errors. Run it now:
1. Click this link: “Download RegHunter” or the blue green below to download RegHunter safety:
Tips: After RegHunter is downloaded, your Chrome /Firefox /IE may display such fake security warning “This type of file can harm your computer. Do you want to keep Download_Reghunter-Installer.exe anyway?“, which is generated by virus to cheat you, please just ignore the fake warning and click “Keep” button.
Notes – If you do not need it any more, please follow instructions on RegHunter uninstall. RegHunter`s free version provides unlimited free scans and detection. After it detects corrupted registry files and system errors files, you can follow the scan results to manually replace them with healthy files copied from healthy PC on your own; or to purchase its full version to automatically fix the Registry and errors with ease. Meanwhile, the full version of RegHunter will offers you great features to optimize your system performance.)
2. Once downloaded, then double-click RegHunter-Installer.exe to start the installation of RegHunter.
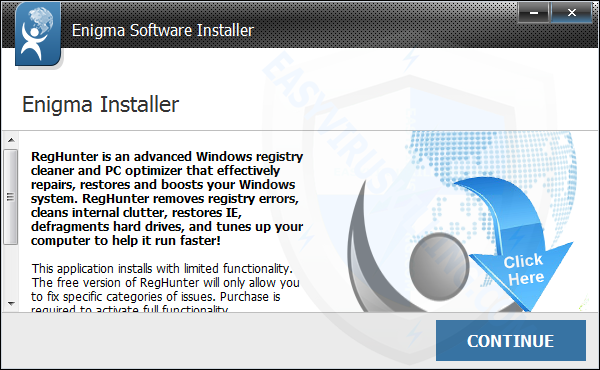
3. When RegHunter is installed, it will be run automatically, then click Scan for Registry Errors Now! to detect files corrupted by 1-855-260-3658 popup:

4. Once RegHunter completes the scan, please click Repair All Errors to solve security bugs related with 1-855-260-3658 popup.
Step 5. Download and install Avast Internet Security to re-scan threats and protect your PC For Free
Avast Internet Security provides 60 Days free trail for you, it’s highly recommended to download and install it to re-scan your system and secure everything in your machine. You can uninstall it when you do not need it any more, it is 100% free. Click the button below to Download Free Avast Internet Security and enjoy 60 days of premium protection for free.

Step 6. Reset Microsoft Edge, Internet Explorer, Firefox and Chrome to clean up cookies of 1-855-260-3658 popup.
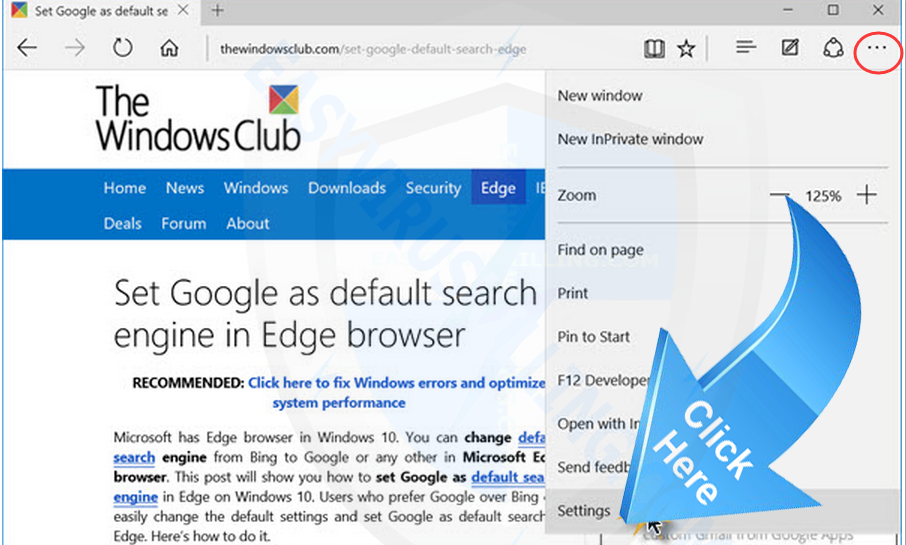
Reset Microsoft Edge
1. Select More (…) on the address bar, then Settings:
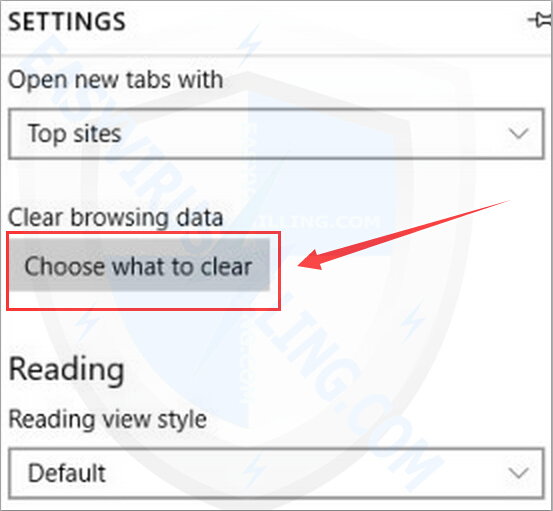
2. click “Choose what to clear”:
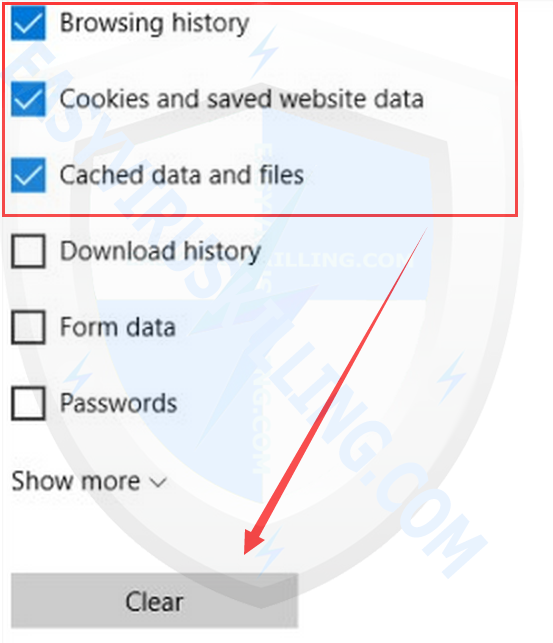
3. Check the first three options and then click Clear:
——————————————————————————————————————————————————————————————-
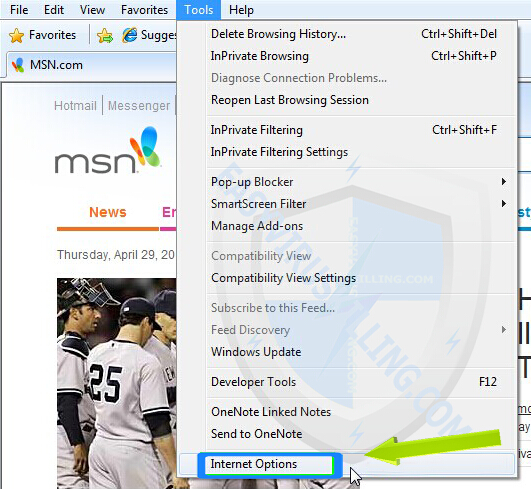
– Reset Internet Explorer
1. Open Internet Explorer, then click on Tools, then click on Internet Options
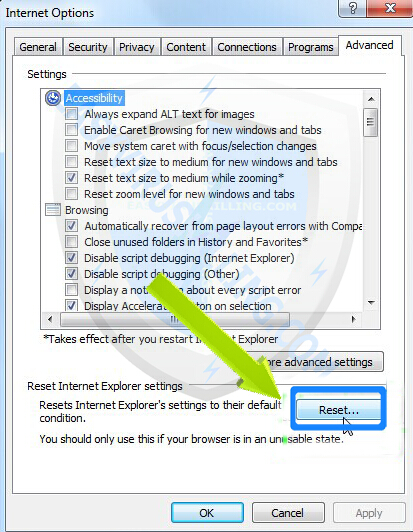
2. On the Internet Options window: click on Advanced tab, then click Reset button
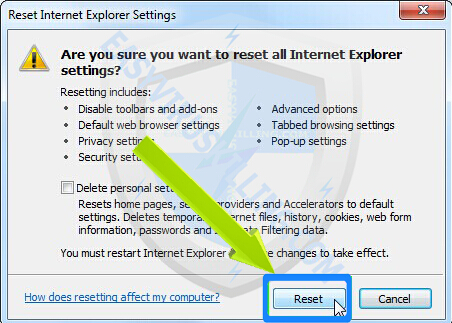
3. A message box will pop up to let you confirm that you want to reset all Internet Explorer Settings, click Reset button when it appears:
4. When the resetting process is done, you’ll see this message box, click Close
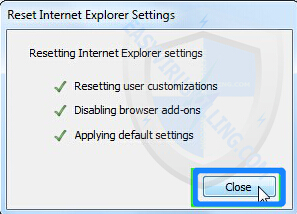
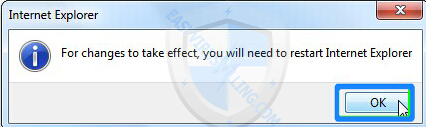
5. You’ll need to restart your Internet Explorer to complete the resetting process.
——————————————————————————————————————————————————————————————-
– Reset Firefox
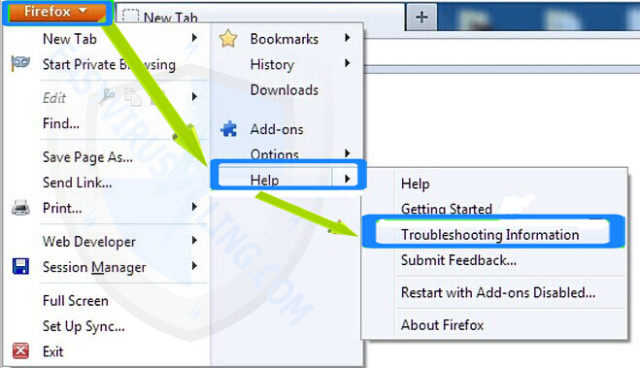
1. Open Firefox, then click on Firefox button, then Click on Help button, then Click on Troubleshooting Information
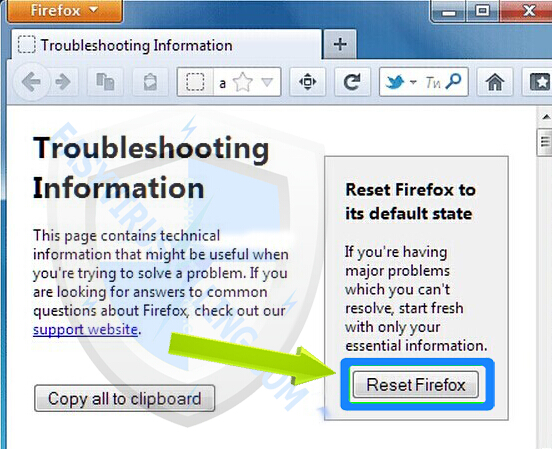
2. At the Troubleshooting Information page, click on Reset Firefox
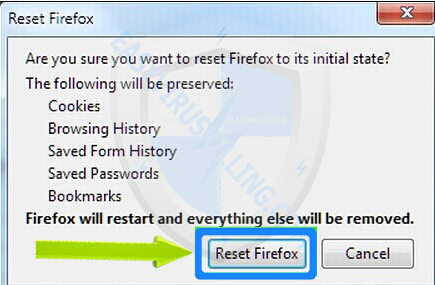
3. A message box will pop up to let you confirm that you want to reset Firefox to its initial state, click Reset Firefox button when it appears:
——————————————————————————————————————————————————————————————-
– Reset Chrome
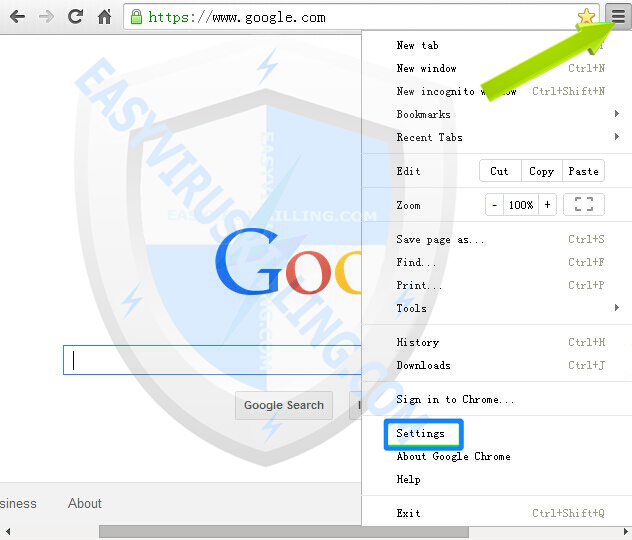
1. Open Chrome, then click “Customize and control Google Chrome” button, and then click on Settings
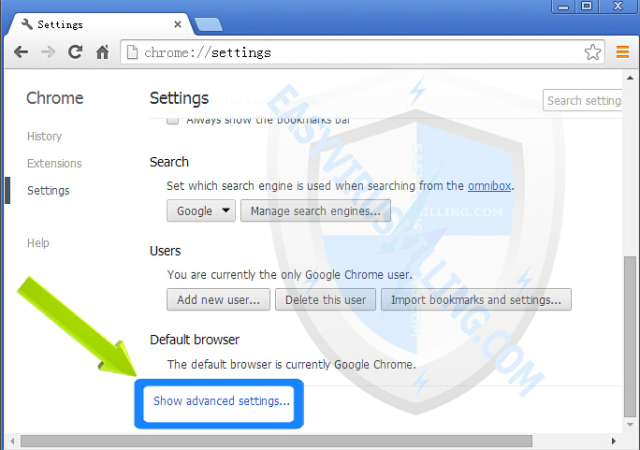
2. Under the Chrome Settings page, scroll down to the bottom, then click on Show advanced settings button
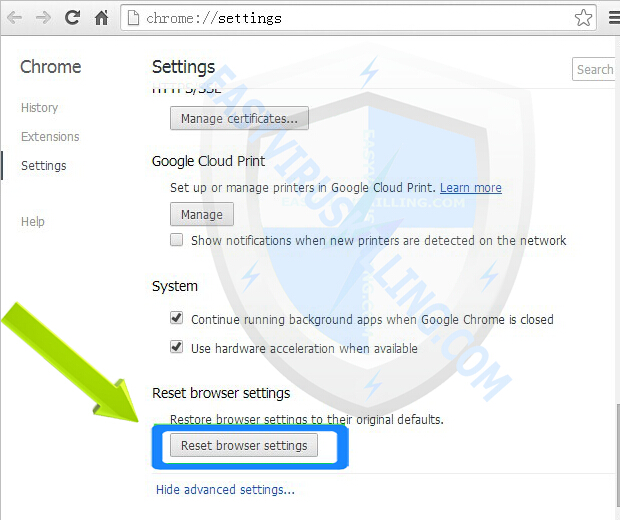
3. After clicking on Show advanced settings button, scroll down to the bottom and click on Reset browser settings button
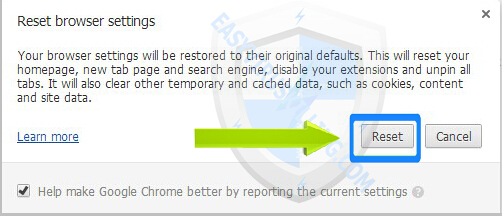
4. A message box will pop up to inform that your browser settings will be restored to their original defaults, click Reset button when it appears:
Section 2 – Effective Steps to Get Rid of 1-855-260-3658 popup from Mac OS
In case your Mac machine has been infected with 1-855-260-3658 popup and related malware, the best and safest way to cure your Mac is to automatically remove the infections with a reliable and powerful protection tool. Here we recommend you to install the famous Mac anti-malware software – MacKeeper Lite, which is capable of cleaning up all Malware, Adware, Trojan, Spyware, Hijacker and other forms of Mac threats and keep your Mac and privacy safe every day. Now get it installed and let it get rid of 1-855-260-3658 popup virus from your Mac completely and speed up your system performance to the top:
1. click the download button below download MacKeeper now:
2. Double-click “MacKeeper.3.8.dmg” and follow its instructions to install it:
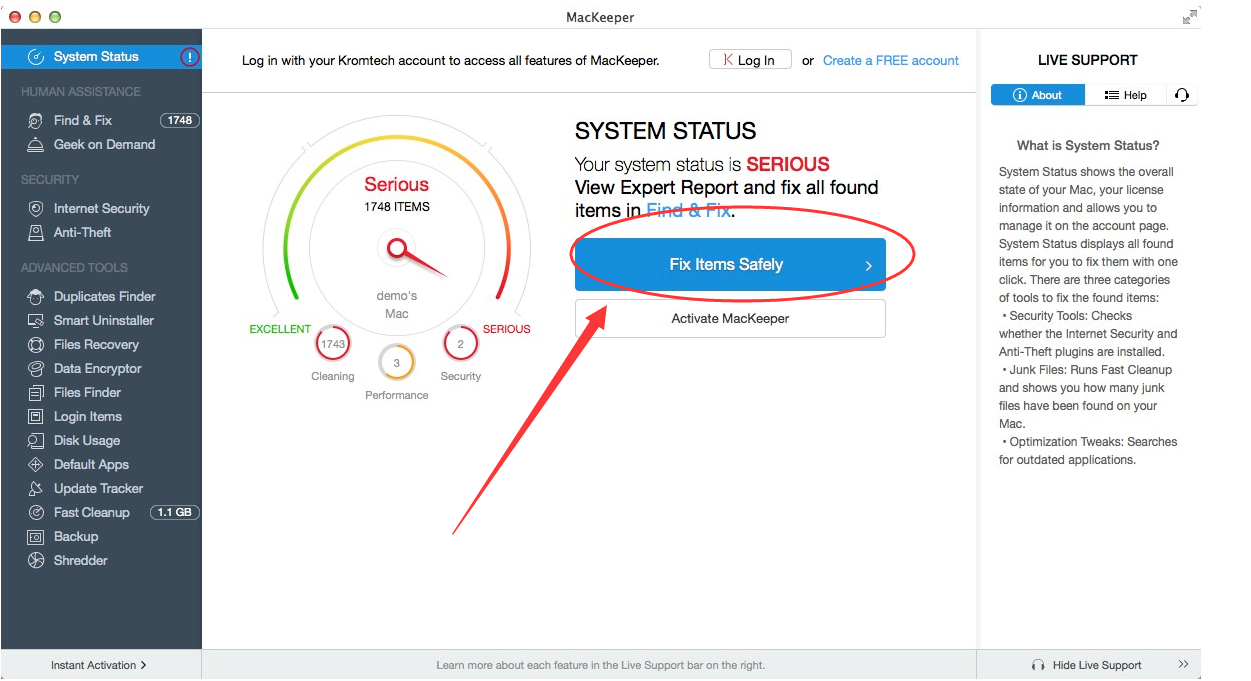
3. In “System Status” tab, run a Scan to detect 1-855-260-3658 popup malware and then click “Fix items Safely” to clean up all infections:
Reasons why millions
of Users Recommend MacKeeper

Tips
1-855-260-3658 popup virus is mainly spread online through resources such as Free Software, Spam Email and Porn Websites. To avoid virus and malware like 1-855-260-3658 popup infect your computer again, you should keep these tips in your mind:
1. Always select Advance or Custom Install if you want to install any free software;
2. Scan all attached files of emails you receive, even the emails sent from Contacts;
3. It’s best not to visit porn websites, which are often hosted by cyber criminal and they may harm your system severely.